May 2, 2026
When Your Business Needs Mobile App Penetration Testing in 2026
Why mobile app penetration testing finds risks web testing misses, real iOS and Android engagement examples, OWASP MASVS, and when your business needs it.
Guides, insights, and practical advice to help your business make smarter security decisions.
Weekly threat intelligence, guides, and practical security advice. No spam.
May 2, 2026
Why mobile app penetration testing finds risks web testing misses, real iOS and Android engagement examples, OWASP MASVS, and when your business needs it.
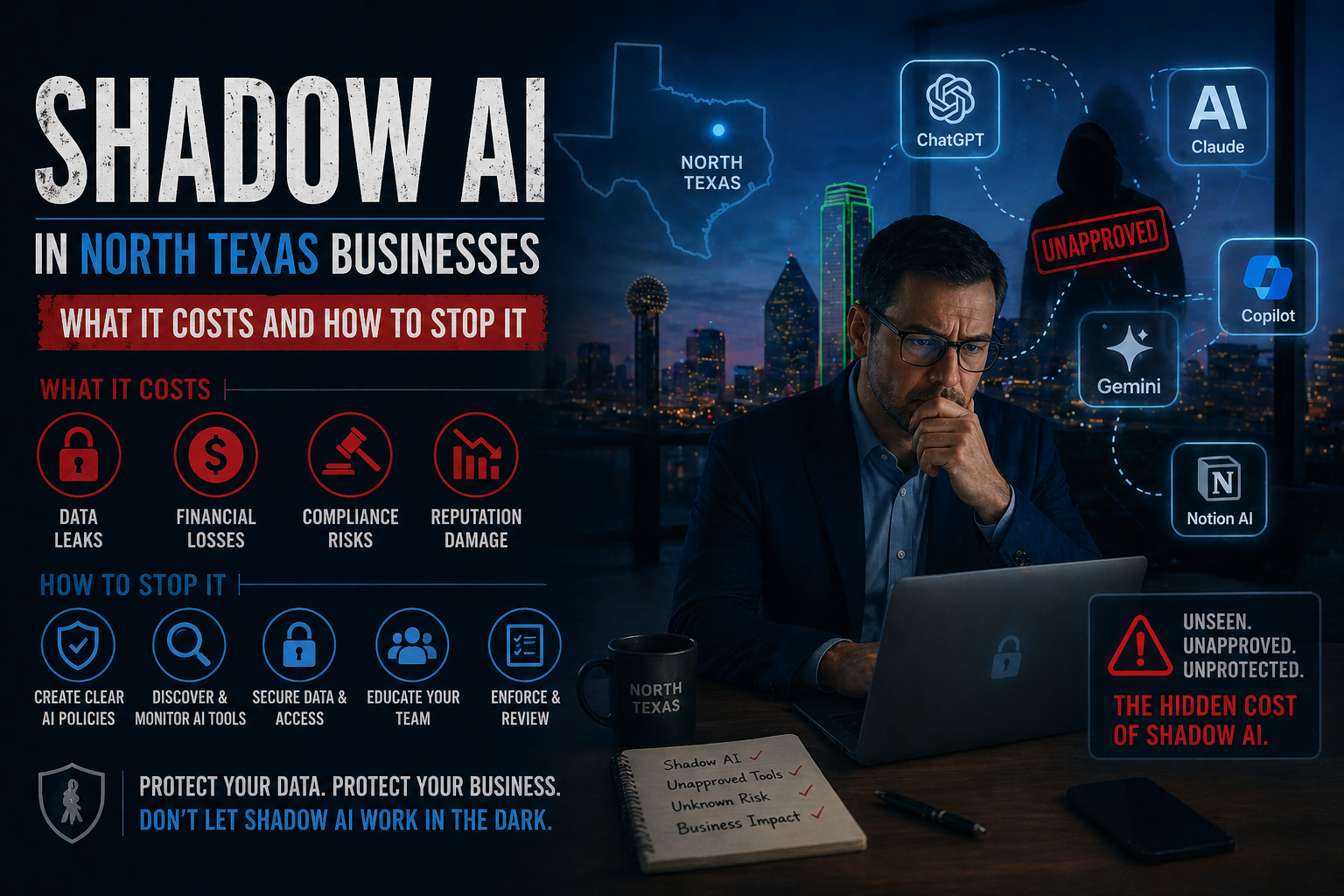
Apr 27, 2026
Shadow AI is the next generation of shadow IT, and most North Texas businesses already have it. Here is what it costs you, how to find it, and what to do this week.
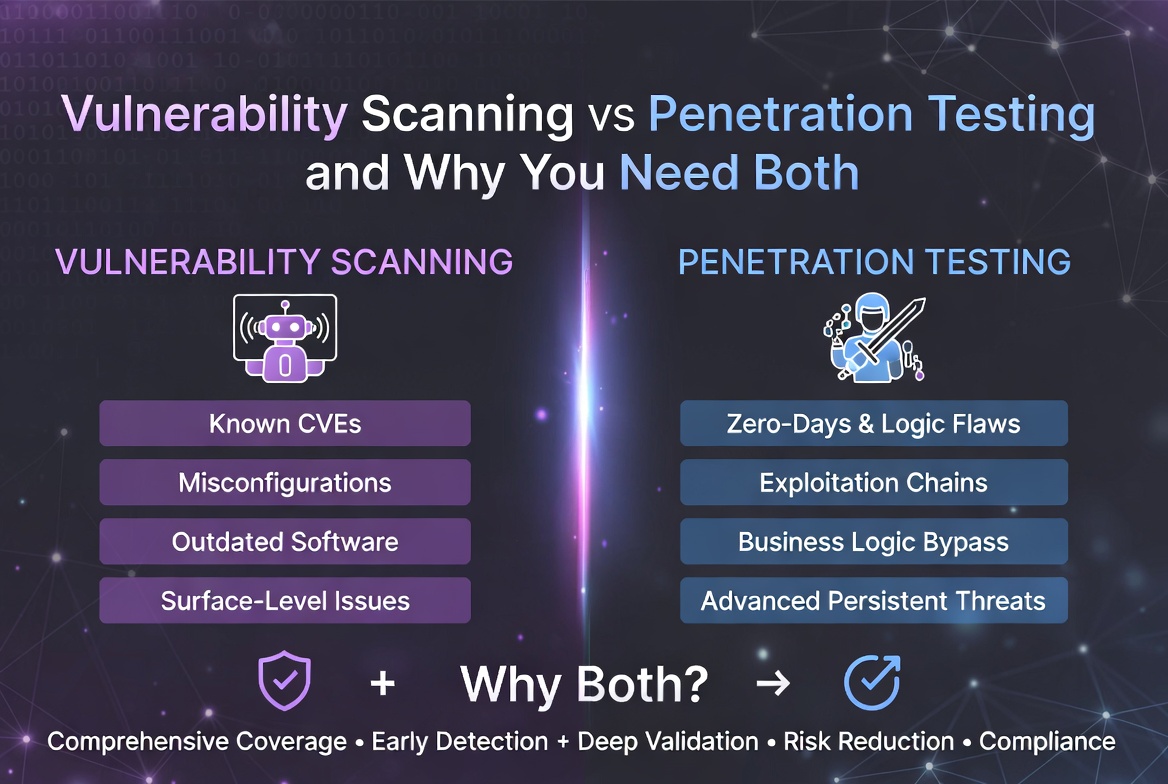
Apr 25, 2026
A plain-English guide to vulnerability scanning, penetration testing, and why most businesses need both running together to actually stay protected.
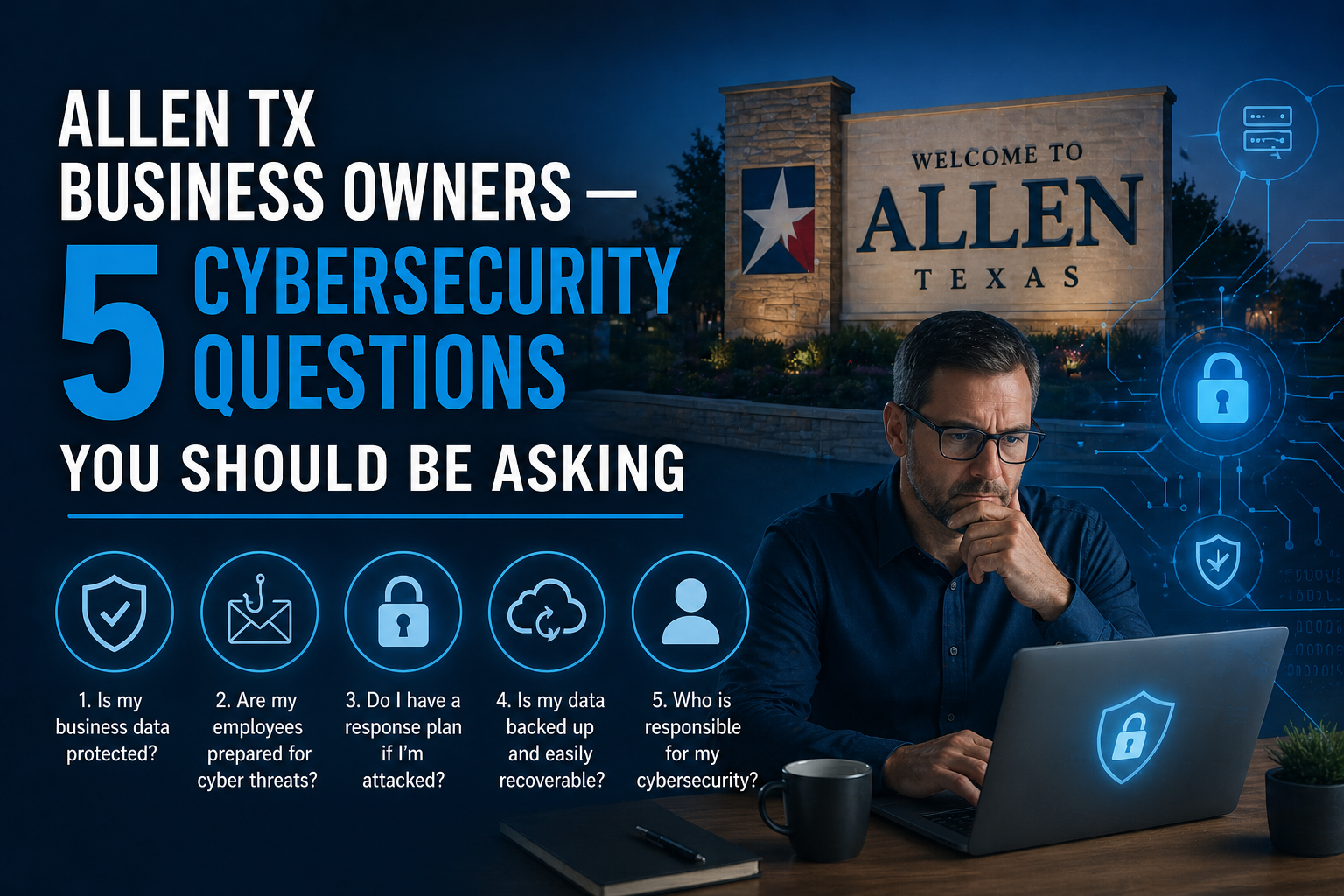
Apr 17, 2026
Five questions every Allen TX business owner should be able to answer about their cybersecurity. If you cannot, it is time to talk to a security professional.

Apr 15, 2026
Frisco is one of the fastest-growing tech hubs in Texas. Here is why the cybersecurity gap is a risk and what local companies should be doing about it.
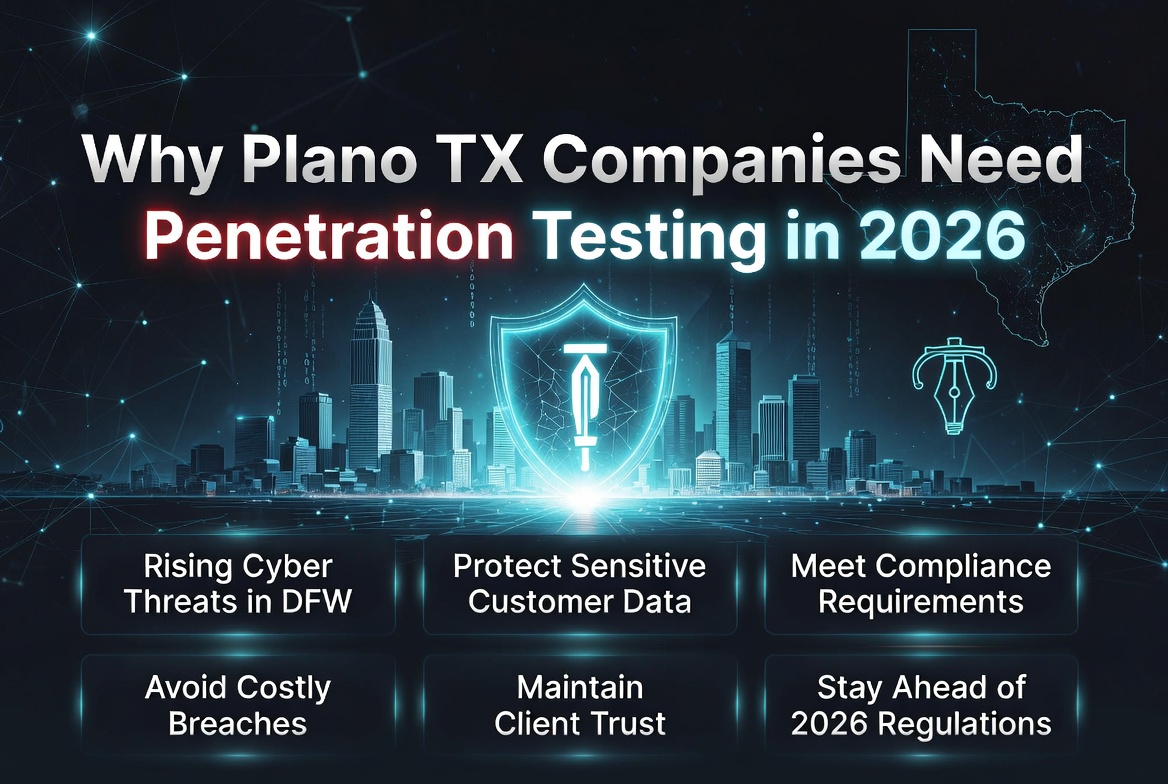
Apr 13, 2026
Plano businesses face enterprise vendor requirements, HIPAA mandates, and targeted attacks. Here is why penetration testing is no longer optional in Plano.

Apr 13, 2026
The software your business trusts every day could be the very thing that lets attackers in. Supply chain attacks are on the rise in 2026, and most businesses have no idea how exposed they are. Here is what you need to know and what you can do about it.

Apr 13, 2026
Ransomware, business email compromise, and supply chain attacks are hitting McKinney businesses hard in 2026. Here is what local companies need to know.

Apr 12, 2026
Mobile app pen testing is a growing market most MSPs cannot serve in-house. Learn how co-managed partnerships let you offer it under your brand without hiring.

Apr 9, 2026
Hardcoded secrets, cleartext traffic, weak crypto, exported components. These are the mobile app vulnerabilities we find most often and how to fix them.

Apr 7, 2026
Social engineering is how most cyberattacks actually begin. Not through some sophisticated hacking technique, but by tricking a real person into making a mistake. This guide explains how these attacks work and what your business can do to stop them.
Our team is here to help. Get a free consultation and find out how Innovation Network Design can protect your business.
Talk to an Expert